Does Your VPN Hide Your Location from Google?
In this short and fun experiment, we’re going to use a VPN to hide our true location, and then we are going to use Google Maps to kick dust in the face of the VPN and reveal our true location.
First up, we need a VPN.
If you already subscribed to a VPN then you can skip this stage. If not, then you can get one for free (for 30 days) here.
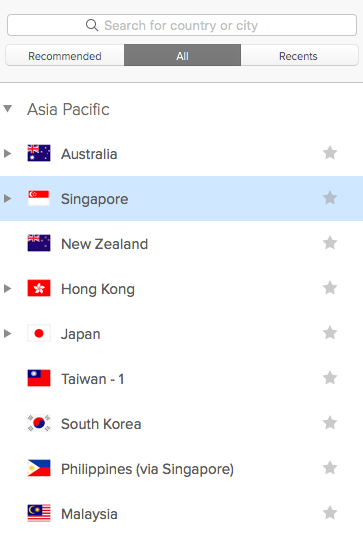
After installing and running ExpressVPN, set your location to somewhere exotic and far away. I went with Singapore, but as you will see there is plenty of choice (90+ countries).
Then go to Google Maps. Initially, Google is going to present you with a local map based on the location you selected when starting up VPN. When I go to Maps, Google reflects my VPN location and presents a map of Singapore.
Because of my VPN settings, the internet thinks I'm in Singapore
This is where the fun starts. Whilst still on the VPN, we’re going to see if Google knows where we actually are (spoiler alert – they actually do).
Still in Google Maps, we’re going to hit the Location button situated bottom right of the screen. This is going to use multiple methods to estimate our true location.
As part of the process, our browser is going to prompt us to ‘Allow’ or ‘Enable’ Location Access. And the answer is yes, we are going to permit this.
And BOOM! Your Location is there!
Google Maps refreshes and a map of our actual location is displayed. As fast as we arrived in Singapore, we’re gone. Singapore is no more. And we’re back to reality. But curiously, we're still on the VPN...
Surprised? Me too. Try it.
Why does this work?
Our true location can be determined in a number of ways, but in this case, it is given away by the set of wi-fi networks that our device can see.
Companies like Google and Apple have been collecting accurate GPS data alongside local wi-fi network data for a while. What this means is that they only need access to the list of networks that your device can see to work out where that device is in the world. This is what you agree to hand over when you opt to 'Allow Location'. Even if you are using a VPN, the networks within shouting distance of your device are telegraphing your actual location.
If you are interested to read about some of the other ways in which your location can be revealed by your browser and phone, there’s a good explanation here.
Long story short… a VPN is going to stop your ISP from seeing what content you are viewing. But Location Services on your workstations and mobile devices is going to give up your true location in a heartbeat. It's SOME privacy, but not TOTAL privacy.
There is an alternative to VPN. And it IS private.
If this kind of privacy leakage is of concern, there is a solution in the form of isolated browsing.
When we implement an isolated browser, we move all browsing activity away from our device. This has a significant number of immediate security and privacy benefits:
No shady, malicious or unvetted third-party code is ever downloaded to our device
Our device cannot become infected with web-borne malware such as ransomware or cryptojacking
All ads, including malicious ones, are blocked
Neither our ISP nor VPN provider can see any of our browsing activity
We can’t be tracked across browsing sessions nor have behavioural profiles built based on our interests
All message attachments (documents) are stripped of potentially dangerous functionality before opening
We can set and forget our passwords and switch to one-click sign-in
Our location remains 100% private as none of the data required to work out where we are is ever handed over to the website (e.g. Google Maps) by the browser
In short, when we use isolated browsing, our location remains private and not even Google can find us.
You can subscribe to an isolated browsing service right now at www.authentic8.com.